Another name of Google hacking is Google dork. We can say that Google hacking is a dictionary of queries through which we can gather sensitive data due to the misconfiguration of the server.
In this article, I am going to show you what is Google hacking. Let's get started
1. Google Hacking The dark side
Search engines like Google use most for a simple purpose: you want to find something on the Internet.
But Google also has a dark side that can be used to track down things on the Internet that are actually not intended for general use: secret documents, passwords, payslips, copyrighted material (films, music, etc.), unprotected security cameras, data breaches or vulnerabilities in web applications. Known as "Google Hacking" or "Google Dorks", anyone can take a look at confidential regions of the Internet within a few minutes. The tools are very simple: With a few additional search parameters, Google's gigantic search index can be “tapped” and information obtained that the respective operator (probably) does not want to reveal to everyone.
But Google also has a dark side that can be used to track down things on the Internet that are actually not intended for general use: secret documents, passwords, payslips, copyrighted material (films, music, etc.), unprotected security cameras, data breaches or vulnerabilities in web applications. Known as "Google Hacking" or "Google Dorks", anyone can take a look at confidential regions of the Internet within a few minutes. The tools are very simple: With a few additional search parameters, Google's gigantic search index can be “tapped” and information obtained that the respective operator (probably) does not want to reveal to everyone.
In this article, I would like to introduce you to a few of these Google search parameters, which can be used to relentlessly make configuration errors and carelessness of operators visible.
2. Foreword
Before you start experimenting with Google’s advanced search parameters, you should consider the following:
“Google Hacking” via Google is initially not prohibited or punishable since the information found on it can be accessed from the Internet without protection. In other words, the operator failed to protect confidential data to a special degree. However, the threshold of crime or crime is quickly exceeded if you misuse the discovered data and vulnerabilities for purposes that cause financial, personal, or damage of any kind to those affected.
Basically, only one thing happens with Google hacking: You use the special search parameters to access Google's databases, which are made publicly available to everyone.
2.1 Why Google hacking works
Due to sometimes blatant configuration errors or missing instructions in the robots.txt, it can happen that Google indexes data or information that is normally not intended for general use. The cause of these configuration errors can usually be traced back to two reasons:
Lack of knowledge: Private individuals in particular often place sensitive data unprotected on an FTP or web server that they operate from home. No security measures are taken or devices (directly) connected to the Internet that neither receive security updates nor are designed for this purpose. If you come across such unprotected data or information, then you should have the decency and report this to the operator - if you can identify it. The rule is: If you do not know what you are doing, you should probably refrain from posting data on the Internet or simply pay someone who is familiar with it.
Inattention: Google hacking not only allows sensitive information from private users to be tracked down, but also explosive, and sometimes secret, documents from companies and institutions. Here it can be assumed that the responsible administrators should normally have sufficient knowledge to avoid such cases. Unpatched web servers, sensitive password lists, or complete backups of business email correspondence, which can be found via Google hacking, paint a different picture. Here we speak of carelessness, gross negligence, and human error.
Google hacking goes back to the year 2002 when Johnny Long found vulnerable or unpatched systems and sensitive information using special search parameters - he himself describes this as Google Dorks. Dork (jerk/idiot) refers to the operators of the website who have not given enough thought to security and do not have their servers under control.
Anyone who believes that the situation has changed by 2017 is extremely wrong. Thanks to the Internet of Things and the increasing number of devices that are connected to the Internet, vulnerable systems can now be detected and sensed information accessed far more frequently than ever before.
2.2 Obtaining information during the pentest
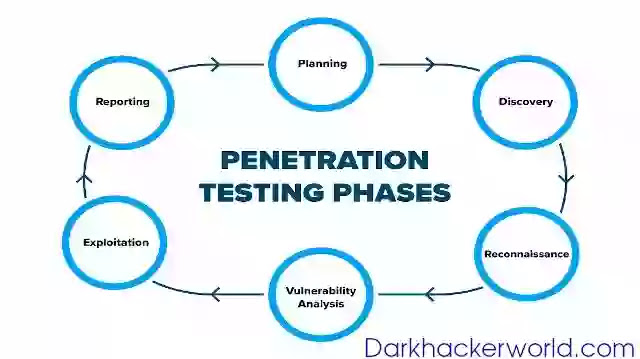
Google hacking has become an indispensable tool for me when performing a penetration test. A penetration test can be divided into different phases, some of which are repeated sequentially.
In the first phase (gathering information), the first step is to collect as much information as possible about the goal that could be of interest for the further course. For this purpose, various publicly available information sources are searched and then evaluated. One of these sources of information is Google or "hacking" via Google.
3. Simple Examples of Google Hacking
Let's start with simple examples and what can be found on the Internet with the special search parameters.
3.1 Video and audio material
Display of websites that make mp3 files publicly available. Be it due to a lack of knowledge, carelessness or even deliberately to offer copyrighted material:
intitle: index of inurl: mp3
intitle: index of inurl: avi
If you then refine your search and add an artist or film title, you can further condense the results.
3.2 Vulnerabilities
The output of SQL error messages is a first indication of the vulnerability to an SQL injection:
Detection of sensitive configuration files that contain MySQL login data such as user names and passwords:
mysqli_connect ext: inc
Representation of vulnerable Apache web servers with a specific version number and system:
intitle: index of "Apache / 2.4.7 (Ubuntu) Server"
inurl: https: // owa
3.3 Sensitive Information/Documents
Detection of (Cisco) VPN access data with which you can gain access to the local network of companies and institutions:
Displaying search results for FTP servers with password files in Microsoft XLS format:
inurl: ftp "password" filetype: xls
Or you search specifically for pages that should have the term "password", "secret", "members" or other expressions directly in the URL:
intitle: index of inurl: password
Search for text files that contain the word "password":
ext: txt intext: password
Display of the (Linux) bash history, which often contains user names for a system:
intitle: index of .bash_history
Display of potentially sensitive Dropbox folders:
intitle: index.of.dropbox
4. Search Parameters
You have already seen some of the most important search parameters used in Google hacking in the examples. I will briefly explain the most commonly used search parameters - these can often be combined wonderfully.
4.1 Basic Parameters
Anyone who has worked closely with the principle of a search engine is probably already familiar with the double-quotes. They ensure that the exact SEARCH word is searched for. If you enter several SEARCH WORDS enclosed in the double quotes, the order is also taken into account:
"SEARCH WORD (or several) SEARCH WORDS"
With site: the search is focused on a specific page. This is useful if you want to limit the search for content, sensitive documents or weak points (SEARCH WORD) to a specific DOMAIN
site: DOMAIN SEARCH
The search parameter cache: in conjunction with a URL shows Google's cached version of the specified website, i.e. the version of the last indexing:
cache: URL
A search with the search parameter intitle: in conjunction with a SEARCH WORD returns results from websites whose title contains this search term. Often used to find pages or directories that have Directory Listing (index of / index.of) enabled:
intitle: SEARCH WORD
allintitle: SEARCH WORDS
With the search parameter intext: in connection with a SEARCH word, websites are displayed in which the term appears in the text of the page:
intext: SEARCH WORD
With allintext: only results are shown that contain all the specified SEARCH WORDS in the text of the page:
allintext: SEARCH WORDS
A search using the search parameter inurl: in conjunction with a SEARCH WORD returns results from websites whose URL contains the search term:
inurl: SEARCH WORD
A search with the search parameter filetype: or ext: restricts the results to documents of a specific FORMAT (e.g. pdf or Docx files):
filetype: FORMAT
Using the search operator related: and specifying a DOMAIN, you can find pages that are similar in content to the specified page.
related: DOMAIN
4.2 Combining search parameters
Incidentally, you can combine the search parameters you just learned with each other. Here are a few examples.
Display of results that have activated directory listing and for which the search word backup occurs within the URL. You will find countless servers or websites on which complete backups of private individuals and companies are sometimes stored unprotected:
intitle: index of inurl: backup
Display of results that have activated directory listing and for which the search word backup occurs within the URL. You will find countless servers or websites on which complete backups of private individuals and companies are sometimes stored unprotected:
intitle: index of inurl: backup
Tracking down WordPress sites that use the WP Security Audit Log plugin and provide the log files unprotected for everyone:
inurl: "wp-security-audit-log" ext: log
Display of websites that provide a vulnerability report, performed by IBM AppScan, unprotected in PDF format. Incidentally, this also works with other vulnerability scanners -explosive details included:
intext: "Web Application Report" intext: "This report was created by IBM Security AppScan" ext: pdf
4.3 Hacking your own website
Apart from refining your search results, you should primarily use Google Hacking to track down your own configuration errors. I have summarized a few standard Google hacks with which you can check your own website. Simply replace <YOUR DOMAIN> with your domain name.
Directories where the directory listing is active:
site: <YOUR DOMAIN> intitle: index.of
Forgotten or unprotected configuration files:
site: <YOUR DOMAIN> ext: xml | ext: conf | ext: cnf | ext: reg | ext: inf | ext: rdp | ext: cfg | ext: txt | ext: ora | ext: ini
site: <YOUR DOMAIN> ext: sql | ext: dbf | ext: mdb
Forgotten or unprotected log files:
site: <YOUR DOMAIN> ext: log
Backups and obsolete / forgotten (backup) files:
Pages that contain "login" in the URL and indicate an area to be protected:
site: <YOUR DOMAIN> inurl: login
The output of SQL error messages. The first indication of SQL injections :
Forgotten or unprotected documents:
The output of phpinfo ():
As you can see, no special " hacker software" is required to find weaknesses or configuration errors on your website. With Google Hacking, you can get a quick overview and pre-empt attackers who don't really mean well with you.
5. Conclusion
Google hacking is legal, but the crime threshold is quickly exceeded. You get curious too quickly and click through the huge amounts of data that Google has indexed. Do not be tempted, because some of the results certainly include honeypots that record and analyze your behavior.
Google Hacking can also detect weaknesses in the IT of (third-party) companies, but you should rather leave this to professional penetration testers, who mostly act on an order-controlled basis. Use the acquired knowledge about Google Dorks to optimize your personal search results or to check your own websites/devices for configuration errors.